We Believe In
Who We Are
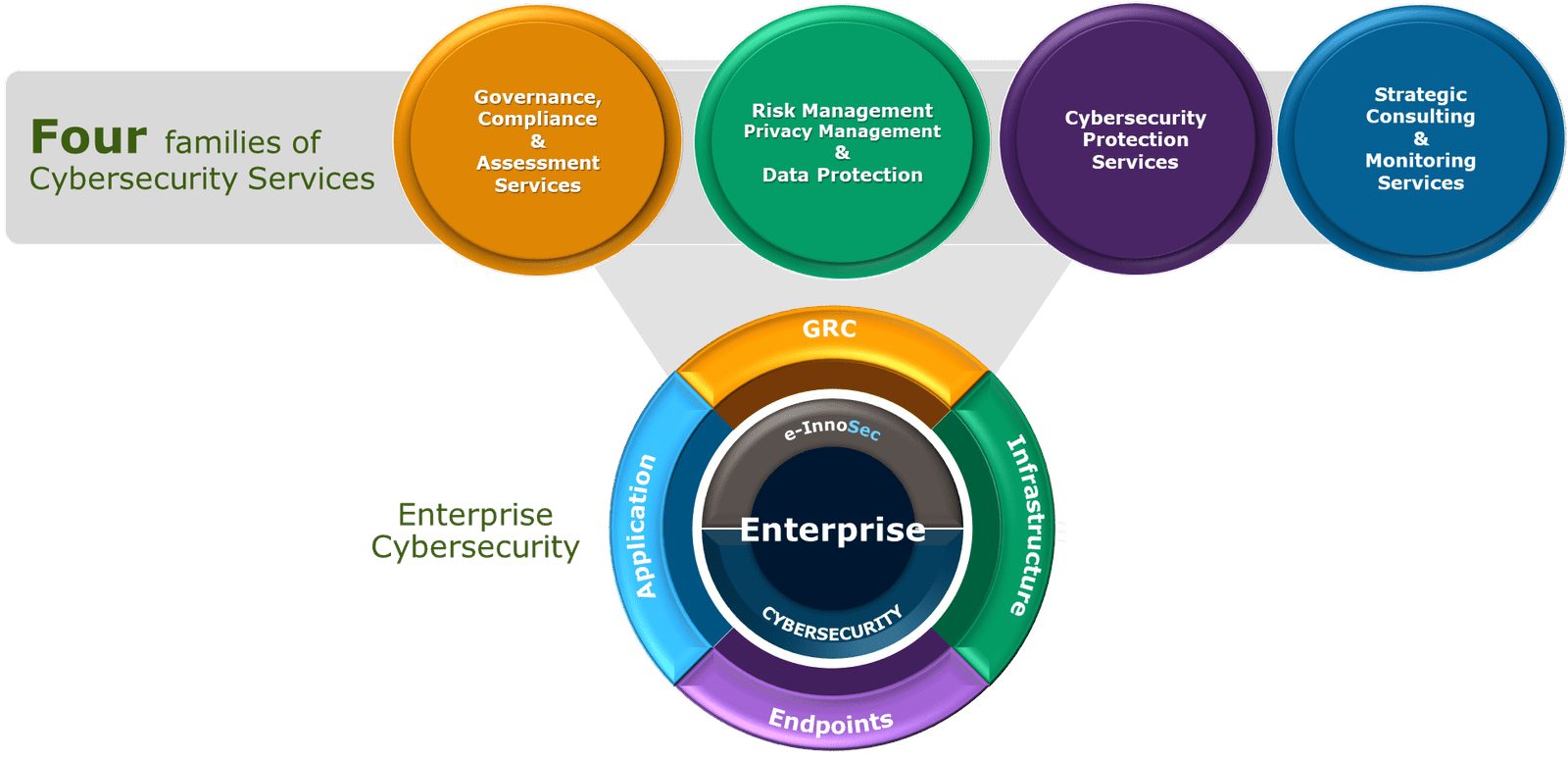
e-InnoSec is a Professional Services and Consulting organization that brings expertise to the clients to supplement their business needs. We are compliance and cybersecurity professionals serving small, midsize, and startup organizations to simplify compliance, transform cybersecurity, and save costs.
The managing team's experience of over 20 years is at the core of designing practical approaches to solving cyber problems, managing risk, selecting frameworks, advising on compliance, and providing automated solutions. Also, we are the only company to support our solutions with free training using the SECURETAIN training platform to ensure scalable and sustainable programs that improve your security posture and achieve compliance objectives.
e-InnoSec services empower organizations to develop a scalable program to manage information security risks and to meet global financial, government, industry, and healthcare mandates such as HIPAA, SOC, PCI, GDPR, CCPA, ISO 27001, NIST, FFIEC and more. We understand cloud security and how to design, implement, and review their deployment for a business. We serve a small ten employee corporation as well as fortune 1000 companies.
Our Story
e-InnoSec Advisory & Consulting Established in January 2015We live in a world where security is what we all strive for, but struggle to find. Up until just recently, security was a very tangible thing meant to protect us from the outside and the unknown. But the world has changed. We do not only need protection; the very ways we conduct business need protection.
Hence, we formed e-InnoSec (Innovative Security), a Compliance and Security company, to protect businesses and help organizations navigate the complex world of cybersecurity and compliance. e-InnoSec is a national service provider to small and mid-size clients, delivering a range of Governance, Risk, Compliance, Audit, and Cybersecurity solutions designed to help our clients meet their information security and compliance objectives and protection needs.
When seeking new talent, the e-InnoSec consulting team says they are looking for employees who are driven, innovative, and willing to take the necessary risks.
What It Is
Better Managed -> Compliance, Risk, Cybersecurity, Business Continuity & Disaster Recovery, and Enterprise Resilience
Why It Matters
Helps To -> Protect Better, Manage Disruption, Reputation, and Customer Confidence.
Where It's Going
Sustainable Success -> High Maturity, Governance, Cyber Culture from the Top, Employee Participation.